Search Results
Showing results 21 to 40 of 42

Patterns in Pixels
Source Institutions
This activity (page 2) draws upon a familiar, computer-based concept related to visual resolution: pixilation.

Program a Friend
Source Institutions
In this activity (on page 2), one person "programs" the other like a robot to move through a space, trying to get them to avoid obstacles and reach a goal.

Human Interface Design: The Chocolate Factory
Source Institutions
In this activity about human interface design issues, learners help the Oompa-Loompas of a great chocolate factory solve different problems.

Secret Writing Devices
Source Institutions
In this activity about encryption, learners cut out a secret decoder badge from a handout and use it to encode messages to each other.

LEGO Robots
Source Institutions
This activity (on page 2 of the PDF under GEMS Activity) is a full inquiry investigation into technology design and testing.

The Muddy City: Minimal Spanning Trees
Source Institutions
In this puzzle, learners investigate the decisions involved in linking a network between houses in a muddy city.
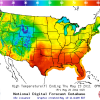
Forward Thinking
Source Institutions
In this activity, learners create their own weather forecast map.

Cipher Wheel
Source Institutions
In this activity, learners make their own encrypted code to pass along secret messages using a printable cipher wheel.
Phylogenetics
Source Institutions
This activity lets learners participate in the process of reconstructing a phylogenetic tree and introduces them to several core bioinformatics concepts, particularly in relation to evolution.

Tourist Town: Dominating Sets
Source Institutions
In this activity, learners use a fictitious map of "Tourist Town" and counters to problem solve how to place ice-cream vans on street intersections so that every other intersection is connected to one

The Turing Test: Conversations with Computers
Source Institutions
This activity aims to stimulate discussion on the question of whether computers can exhibit “intelligence,” or are ever likely to do so in the future.

What am I?
Source Institutions
In this activity, learners examine nanoscale structures of common things.

Cryptographic Protocols: The Peruvian Coin Flip
Source Institutions
This activity about cryptographic techniques illustrates how to accomplish a simple, but nevertheless seemingly impossible task—making a fair, random choice by flipping a coin between two people who d

Unlocking the Secret in Product Codes
Source Institutions
In this activity, learners will explore how product barcodes are scanned accurately and be able to "guess" the last number in a 13 digit barcode correctly every time.

Artificial Intelligence: The Intelligent Piece of Paper
Source Institutions
This activity explores what it means for a computer to be intelligent and introduces the topic of what a computer program is and how everything computers do simply involves following instructions writ

Ice Roads: Steiner Trees
Source Institutions
In this outdoor activity, learners use pegs (like tent pegs) and string or elastic to simulate drill sites and roads in Northern Canada.

The Orange Game: Routing and Deadlock in Networks
Source Institutions
When a lot of people share one network (such as cars using roads, or messages getting through the Internet), there is the possibility that competing processes will create a “deadlock," or an interrupt

Information Hiding: Sharing Secrets
Source Institutions
This activity about cryptographic techniques illustrates a situation where information is shared, and yet none of it is revealed.

Beat the Clock: Sorting Networks
Source Institutions
Even fast computers are limited to how quickly they can solve problems. One way to speed things up is to use several computers at once.
Hand Biometrics Technology
Source Institutions
In this activity, learners explore how engineers incorporate biometric technologies into products as well as the challenges of engineers who must weigh privacy, security and other issues when designin
