Search Results
Showing results 1 to 20 of 22

Public Key Encryption: Kid Krypto
Source Institutions
In this activity, learners conduct a simulation exercise related to public key encryption and try to intercept a message sent between two learners.

Electric Messages: Then and Now
Source Institutions
In this activity, learners explore electronic communication, the Morse Code system, and advances all the way through text messaging. Learners build a simple circuit, send messages to one another.
Solving Playground Network Problems
Source Institutions
In this activity, learners use cooperation and logical thinking to find solutions to network problems on the playground.

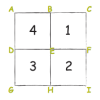
Passion for Pixels
Source Institutions
In this technology activity, learners explore digital imaging and pixels. Learners "transmit" an image to a partner by creating an image on grid paper.
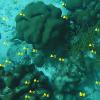
Coral Snapshots: Biodiversity in Marine Protected Areas
Source Institutions
In this data activity, learners analyze data from coral reef snapshots taken by scientists at the Virginia Institute of Marine Science.
Sound Representation: Modems Unplugged
Source Institutions
In this activity, learners listen to songs and decode hidden messages based on the same principle as a modem. As a final challenge, learners decode the binary messages in a music video.

Locating a Point
Source Institutions
In this activity, learners work in teams to simulate the process used by Global Positioning Systems (GPS) to determine the location of a fallen meteorite in Antarctica.

EEEEK--A Mouse!
Source Institutions
In this activity, learners explore the concept of how engineering solved the problem of human/computer interface.

Arduino Blink Challenge
Source Institutions
In this activity, learners explore computer programming and the impact of computers on society. Learners build and test a program to turn a light on and off using an Arduino board.

Human Interface Design: The Chocolate Factory
Source Institutions
In this activity about human interface design issues, learners help the Oompa-Loompas of a great chocolate factory solve different problems.

Slide Rules
Source Institutions
Learners make their own simple slide rules out of paper and learn how they work.

Secret Writing Devices
Source Institutions
In this activity about encryption, learners cut out a secret decoder badge from a handout and use it to encode messages to each other.

Tracking Otters
Source Institutions
This activity (on pages 38-43) has learners simulate the way scientists track and map the movement of otters in the wild using radio trackers.

Rover Races
Source Institutions
In this activity, learners experience some of the challenges of "tele-operating" a robotic vehicle on another planet when they design and execute a series of commands to guide a human "rover" through

Cipher Wheel
Source Institutions
In this activity, learners make their own encrypted code to pass along secret messages using a printable cipher wheel.
Puzzled Partners
Source Institutions
In this web-based activity, learners try to figure out who in an online chat room has their matching puzzle piece.

The Turing Test: Conversations with Computers
Source Institutions
This activity aims to stimulate discussion on the question of whether computers can exhibit “intelligence,” or are ever likely to do so in the future.

Cryptographic Protocols: The Peruvian Coin Flip
Source Institutions
This activity about cryptographic techniques illustrates how to accomplish a simple, but nevertheless seemingly impossible task—making a fair, random choice by flipping a coin between two people who d

Artificial Intelligence: The Intelligent Piece of Paper
Source Institutions
This activity explores what it means for a computer to be intelligent and introduces the topic of what a computer program is and how everything computers do simply involves following instructions writ

Information Hiding: Sharing Secrets
Source Institutions
This activity about cryptographic techniques illustrates a situation where information is shared, and yet none of it is revealed.
