Search Results
Showing results 1 to 20 of 31
From the Internet to Outer Space
Source Institutions
In this activity, learners will use Google Sky to observe features of the night sky and share their observations.

Public Key Encryption: Kid Krypto
Source Institutions
In this activity, learners conduct a simulation exercise related to public key encryption and try to intercept a message sent between two learners.
Space Weather Action Center
Source Institutions
In this interdisciplinary activity, learners create a Space Weather Action Center (SWAC) to monitor solar storms and develop real SWAC news reports.

The Poor Cartographer: Graph Coloring
Source Institutions
In this activity, learners help a poor cartographer color in the countries on a map, making sure each country is colored a different color than any of its neighbors.

Count the Dots: Binary Numbers
Source Institutions
Data in computers is stored and transmitted as a series of zeros and ones. Learners explore how to represent numbers using just these two symbols, through a binary system of cards.

Color by Numbers: Image Representation
Source Institutions
Computers store drawings, photographs, and other pictures using only numbers. Through this activity, learners decode numbers to create pictures using the same process that computers use.

Programming Languages: Marching Orders
Source Institutions
In this activity about computer programming, learners follow instructions in a variety of ways in order to successfully draw figures.

Passion for Pixels
Source Institutions
In this technology activity, learners explore digital imaging and pixels. Learners "transmit" an image to a partner by creating an image on grid paper.
Sound Representation: Modems Unplugged
Source Institutions
In this activity, learners listen to songs and decode hidden messages based on the same principle as a modem. As a final challenge, learners decode the binary messages in a music video.

EEEEK--A Mouse!
Source Institutions
In this activity, learners explore the concept of how engineering solved the problem of human/computer interface.

Binary Code Bracelets
Source Institutions
In this activity, learners make their own binary code bracelets by translating their initials into 0s and 1s represented by beads of 2 different colors.

Patterns in Pixels
Source Institutions
This activity (page 2) draws upon a familiar, computer-based concept related to visual resolution: pixilation.

Program a Friend
Source Institutions
In this activity (on page 2), one person "programs" the other like a robot to move through a space, trying to get them to avoid obstacles and reach a goal.

Human Interface Design: The Chocolate Factory
Source Institutions
In this activity about human interface design issues, learners help the Oompa-Loompas of a great chocolate factory solve different problems.

Secret Writing Devices
Source Institutions
In this activity about encryption, learners cut out a secret decoder badge from a handout and use it to encode messages to each other.

LEGO Robots
Source Institutions
This activity (on page 2 of the PDF under GEMS Activity) is a full inquiry investigation into technology design and testing.

The Muddy City: Minimal Spanning Trees
Source Institutions
In this puzzle, learners investigate the decisions involved in linking a network between houses in a muddy city.
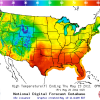
Forward Thinking
Source Institutions
In this activity, learners create their own weather forecast map.

Cipher Wheel
Source Institutions
In this activity, learners make their own encrypted code to pass along secret messages using a printable cipher wheel.

Tourist Town: Dominating Sets
Source Institutions
In this activity, learners use a fictitious map of "Tourist Town" and counters to problem solve how to place ice-cream vans on street intersections so that every other intersection is connected to one
